In this project, we will be showing you how to setup Raspberry Pi SSH keys. It’s the perfect way to harden your Pi’s security.
If you have root access to the server, the easy way to solve such problems is to run sshd in debug mode, by issuing something like /usr/sbin/sshd -d -p 2222 on the server (full path to sshd executable required, which sshd can help) and then connecting from the client with ssh -p 2222 user@host. In order to provide a public key, each user in your system must generate one if they don’t already have one. This process is similar across all operating systems. First, you should check to make sure you don’t already have a key. By default, a user’s SSH keys are stored in that user’s /.ssh directory. You can easily check to see if you have a key already by going to that directory.
Using SSH Keys for authentication is an excellent way of securing your Raspberry Pi as only someone with the private SSH key will be able to authenticate to your system.
- How to Generate a Public/Private Key Pair for Use With Solaris Secure Shell. Users must generate a public/private key pair when their site implements host-based authentication or user public-key authentication. For additional options, see the ssh-keygen(1) man page. Before You Begin.
- Jun 22, 2012 SSH keys provide a more secure way of logging into a server with SSH than using a password alone. While a password can eventually be cracked with a brute force attack, SSH keys are nearly impossible to decipher by brute force alone. Generating a key pair provides you with two long string of characters: a public and a private key.
- The SSH key needs to be added to Bitbucket Server, and your Bitbucket Server administrator must have enabled SSH access to Git repositories, before you can make use of the key. Bitbucket Server supports DSA, RSA2, and Ed25519 key types. RSA1 is not supported.
- Oct 20, 2014 The first step to configure SSH key authentication to your server is to generate an SSH key pair on your local computer. To do this, we can use a special utility called ssh-keygen, which is included with the standard OpenSSH suite of tools. By default, this will create a 2048 bit RSA key pair, which is fine for most uses.
Hi i am using solaris 10.I am trying to setup a public/private key but it is not working.Appreciate your repsonse on it There are two servers DB1 server and DB2 server. 1)I have generated public/priva The UNIX and Linux Forums.
This works by generating an SSH Key pair, you will retain the SSH private key, but the public key will go onto the Raspberry Pi’s operating system.
These SSH keys act as a means of identifying yourself to the SSH server using public-key cryptography and challenge-response authentication.
If you value your security SSH Keys is something you should set up, it offers a few security benefits over password authentication.
For starters, it is much harder for an attacker to be able to intercept and is also much more complicated to brute force. A standard SSH Key is usually 2048 characters long, compared to a password that is no longer than 32 characters.
Equipment List
Below are all the pieces of equipment that I made use of for this Raspberry Pi SSH Keys Authentication tutorial.
Ubuntu Ssh Key Generation
Recommended
Raspberry Pi 2 or 3
Micro SD Card
Power Supply
Ethernet Cord (Recommended) or Wifi dongle (Pi 3 has Wifi inbuilt)
Optional
Raspberry Pi Case
Generating SSH Keys on Windows
To generate SSH keys on a Windows-based operating system, we will have to rely on a piece of software called PuTTY.
You can download PuTTY from their website. Make sure you get the full package version as this includes the piece of software that we need to generate the SSH Keys for your Raspberry Pi.
1. Once you have downloaded and installed PuTTY to your computer go ahead and open up the program that was installed alongside it called PuTTYgen.
2. With PuTTYgen opened on your computer, click the “Generate” button as we have shown in the image below.
Pressing this button will generate the public and private SSH keys that we will use to make our SSH connection to our device, in our case this will be the Raspberry Pi.
3. Once PuTTYgen has begun generating the SSH keys it will ask you to move your mouse in the space as we have indicated in the image below.
By doing this, it helps ensure that the SSH key it generates should be genuinely unique and be hard for someone to be able to generate the same key quickly.
4. With the SSH keys now generated, there are a few more things that you need to do.
The first (1.) is to set a name for this SSH key, make this something memorable, so you know what SSH key is required when connecting.
Secondly (2.) you should set a passkey, this ensures that even if someone managed to steal your private SSH key, they would still need to enter a password.
This passkey acts as a second line of defense. If you would prefer not to have to enter a password at all, then you can skip this step and leave the two fields empty.
However, we do not recommend doing this if you value your security.
Thirdly (3.) we need to save the public key and the private key to somewhere safe on the computer. Make a note of the location that you save both of these files as you will need these to make a connection to your Raspberry Pi. Also, make sure you end the files in .ppk so that PuTTY can pick them up.
Finally (4.) copy down the public SSH key that is featured in the text box shown in the image below. You can quickly select all the text by clicking on the box and pressing CTRL + A then CTRL + C.
We will need this text shortly to add to our Linux systems SSH Authorized keys file. Without this, the system won’t be able to see our private key as a proper authentication method.
5. The next steps of this tutorial will walk you through the process of copying the public SSH key to your linux device. In our case, we will be using a Raspberry Pi that is running the Raspbian operating system.
Nwow you can proceed to the section titled “Copying the Public Keys manually” to continue with this Raspberry Pi SSH Keys tutorial.
Generating SSH Keys on Linux based systems
1. Generating SSH keys on a Linux system is a little easier as the SSH tools to do this are usually included with the main operating system. This means we do not have to install any additional packages.
To generate SSH Keys open up a terminal session on your Linux device enter the following command.
2. With the ssh-keygen tool now running you will be first asked to enter a file in which to save the key. For this tutorial, just press Enter to leave this as the default.
Since we are doing this on our Raspberry Pi Raspbian installation, this default directory was located at /home/pi/.ssh/id_rsa.
3. After setting the file in which to save the key we now need to decide whether we want to use a passphrase.
Personally, we recommend that you utilize a passphrase as it ensures that your private key will have a bit of extra security.
This additional security means that even if someone manages to steal the file as they will need to enter the passphrase to decrypt the private key.
So at this step enter a passphrase (Make sure that this is something secure but memorable).
Key generator works smoothly without any issues at all, updated daily, all the keys are valid and unique. Almost every time a store opens up, you can expect some giveaways from them to get more customers and fans. We are all together made this phenomenal key code generator to help gamers all around the world. Thanks to our site and our key generator program you can get totally free cd key easily without having to look for hours where the contest is and what the terms are.We’ve partnered with the CD key price comparison websites and some online cd key stores. 
Alternatively, if you do not like having to enter a password, you can press Enter but remember this means that anyone who has your private key can access your device without entering any password.
4. Now you have the choice to either copy your SSH public key by utilizing the ssh-copy-id tool or manually copy the key itself.
If you want to copy the key over manually, then follow step 5 and step 6, otherwise skip to the next section titled “Copying the Public Key using SSH Tools“.
5. The SSH key should now be generated so we can grab the contents of the public key file, we will need the contents of the file for setting up authentication on the device we want to use the SSH keys to authenticate to.
To get the contents of the public key, you can utilize the following command on your Linux based device.
6. With the contents of the public key now handy we can now proceed to the next step of actually adding the SSH key to the authorized_keys file.
Now skip to the section titled “Copying the Public Keys manually” to learn how to utilize the public keys contents to allow the private key to act as an authorization key.
Copying the Public Key using SSH Tools
1. On your Linux device (In our case it’s one of our Raspberry Pis), run the following command. Make sure that you replace IP_ADDRESS with the IP address of the remote machine that you want to copy the keys to.
Please note that you will be asked to log in with both your username and password for that remote machine as the tool needs these to copy over your public key.
Once done, this tool will automatically add your public key to the authorized_keys file on the remote machine.
Copying the Public Keys Manually
1. Back on the Raspberry Pi, we need to utilize a few commands to setup our authorized_keys file. This is the file that the SSH daemon will check when a private key is used for authentication.
To begin let’s create the folder that our authorized_keys file will be sitting in. To do this, we will be using the install command with a few parameters to set the correct permissions.
Run the following command on your Raspberry Pi.
2. With the folder created let’s go ahead and put our public key in the authorized_keys file.
To do this run the following command to begin editing it.
3. In this file copy and paste the contents of the public SSH key that you generated earlier using either your Windows device or your Linux device.
SSH will authenticate any private keys against the public key present to see if it is a legitimate connection to authorize.
4. Once you have your public SSH key entered into the authorized_keys file, you can save and quit out of the file by pressing Ctrl + X then Y and finally Enter.
5. With the file now saved we need to make sure it has the correct permissions. To do this, we need to run the following commands.
These commands will assign the correct permissions to the file so that it can be read by SSH when you try to log in.
If you are not using the default “pi” user on Raspbian make sure you replace the text “pi” in the following command with the name of the user you want to use this for authentication.
6. With the SSH private key now saved and the permissions correctly set we can now proceed to login. We will do this before we disable password authentication, so we do not lock ourselves out of our Raspberry Pi.
For our SSH key authentication tutorial, we will be showing you how to connect to your Raspberry Pi using your private key and PuTTY.
Connecting using your Private Key on Linux
1. Utilizing the private key is dead easy on the Linux device that you generated the key in the first place.
The SSH tool by default on most Linux based systems is designed to automatically make use of the private key when attempting to make a connection.
As long as you are using the machine you used to generate the private key, you can use the SSH command as shown below.
The system will automatically try to use the private key that we created earlier to make the connection.
Thanks to copying the public key into the authorized_keys file of the remote host, it will be able to recognize our incoming private key and accept our connection.
2. If you set a passphrase, you will now be asked to enter that before you can continue, this is required to unlock your private key.
After entering your passphrase, you should now be logged into the remote machine.
If you don’t like having to enter your passphrase every time, don’t worry as we will go into how to cache this later on in the tutorial.
Connecting to your Raspberry Pi using a Private Key with PuTTY
1. In this section of the Raspberry Pi SSH keys tutorial, we will be showing you how to use your private key with PuTTY to connect to the Raspberry Pi.
Connecting using a private key is a relatively simple process.
Start by opening up PuTTY on your computer and entering your Raspberry Pi’s IP address (1.) then click on “Auth” under the “SSH” section (2.)
2. Next, you need to press the “Browse” button. This button will allow you to find and select the private key that we saved earlier in the tutorial. Selecting this file will allow PuTTY to try and use it for authentication.
After you have selected the private key from the browser, you should now press the “Open” button to start the connection.
3. Upon connecting you will be first asked to enter a username, Make sure this is the username that belongs to the private key that you are using otherwise authentication will fail.
After entering the correct username, you will be now asked to enter a passphrase for your private key if you set one earlier.
Upon entering a correct passphrase you will be logged into the SSH session. You can now proceed to disabling password authentication completely.
Removing Password Authentication
1. To disable password authentication, we need to modify the sshd_config file. Within this file, we can change the behavior of the SSH daemon.
To modify this file run the following command on your Raspberry Pi.
2. Within this file, we need to find the following line and change “yes” to “no“.
This simple change will completely disable the ability to login to your Raspberry Pi with just a password. From now on you will require the private key to gain access to the system through SSH.
If you are having trouble finding the line you can use CTRL + W to find it quickly. (If you’re using the nano editor)
Find
Replace with
3. You can now save and quit out of the file by pressing CTRL + X then Y and finally ENTER.
4. With the changes now made to the sshd_config file, we should restart our Raspberry Pi to ensure the changes are loaded in.
Remember to make sure that your private key is allowing you to connect to your Raspberry Pi as passwords won’t work after restarting.
Once you are happy with everything, use the following command on your Raspberry Pi to restart it.
5. If everything is working correctly you should only be able to perform an SSH connection if you have a valid private key.
Without the private key, the connection will be refused by the SSH agent. As you can no longer use your password, keeping your private key safe is a very crucial task as it is now your only way of remotely accessing your device.
If for some reason you manage to lose your private key or forget the passphrase for your private key there is still one way of gaining access to your device.
To fix any issues that may arise with your SSH connection you can still physically connect a keyboard and mouse to your device to regain control.
To restore password access over the SSH connection, you should try reverting the change we made to the PasswordAuthentication setting and then refollow the tutorial to set up the SSH keys again.
Caching SSH Passphrase for the Current Terminal Session
1. If you are using the SSH bash tool, then you can cache the passphrase for your private key while the current session is still going.
To do this, we must first start up another session of the ssh-agent. We can do this by running the following command within the terminal session.
Upon entering this command, you will be shown a process id for the ssh-agent that we just loaded. You can use this process id later on to kill the agent and remove the passphrase caching.
The process id should appear something like, “Agent pid 26484“, you need to make a note of the number.
Ssh Key Generation Windows
2. Now that we have started up our additional session of the ssh-agent let’s go ahead and add our private key to it.
We can do this by just typing in the following command, be prepared to enter your private key’s passphrase.
3. With your SSH key now added to the agent, you should be able to login to any remote machine that has your key authorized without needing to enter your passphrase.
4. To remove your private key from the SSH-agent cache, you will need to kill the ssh-agent we started earlier.
The easiest way to do this is to make use of the process id that we grabbed earlier. Just insert that process id after the command ‘kill’ to kill the process.
Jul 31, 2012 If the MachineKey isn't configured in the web.config, where does the default value get pulled from? I checked the Machine.config for ASP.NET 4.0 and it wasn't there. My team wants to set this value at a higher level than the web.config in case one of our developers forgets to add the machine key to the web.config. The all-in-one ultimate online toolbox that generates all kind of keys! Every coder needs All Keys Generator in its favorites! It is provided for free and only supported by ads and donations. 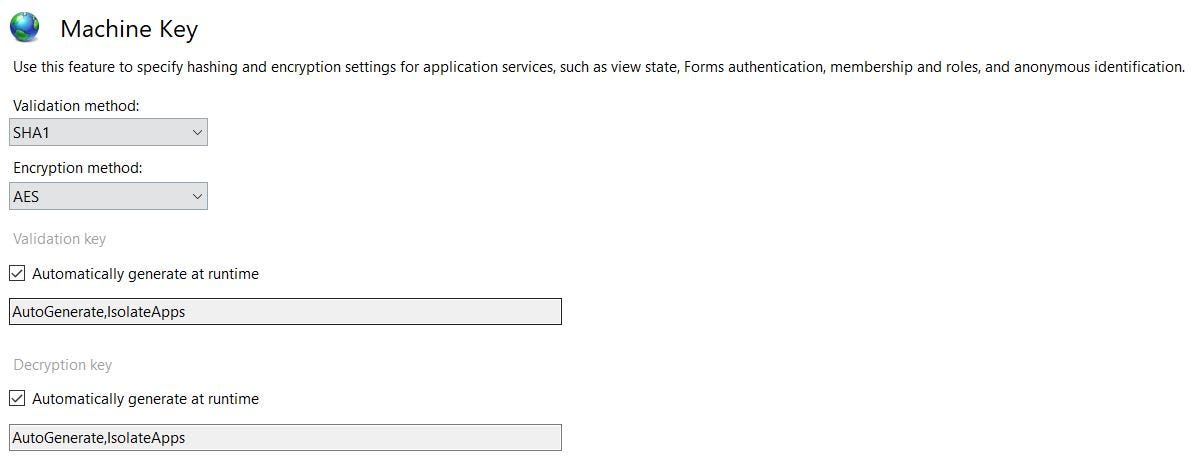 Oct 22, 2019 For ASP.NET framework ≥ 4.5, we need to supply the decryption algorithm and the decryption key to the ysoserial payload generator as. Machine key generating closed. Machine Key Generator. How to delete old cookies after changing to manual machine key and wildcard cookies ASP.NET MVC 4.5. Reason 5 licence number generator serial numbers, cracks and keygens are presented here. No registration is needed. Just download and enjoy.
Oct 22, 2019 For ASP.NET framework ≥ 4.5, we need to supply the decryption algorithm and the decryption key to the ysoserial payload generator as. Machine key generating closed. Machine Key Generator. How to delete old cookies after changing to manual machine key and wildcard cookies ASP.NET MVC 4.5. Reason 5 licence number generator serial numbers, cracks and keygens are presented here. No registration is needed. Just download and enjoy.
I hope by the end of this Raspberry Pi SSH keys tutorial that you learned how to both generate and authenticate by using SSH keys. If you have any thoughts, tips or anything else that you would like to mention then please don’t hesitate to leave a comment below.